"Silker AI caught a zero-day exploit in our production API before it could cause damage. The AI-powered detection saved us from a major breach."
Protect Your Web App.Zero Code Changes.
Deploy Silker as a reverse proxy in front of your application. AI-powered threat detection, automatic API schema learning, and real-time blocking. Works with any stack.
Deploy Anywhere
One proxy, any infrastructure. No code changes required.
Your app can be on
Run the proxy elsewhere; point target to your deployment.
Protects Any Stack
Reverse proxy works with every language and framework
Works as a reverse proxy — no SDK, no code changes, no vendor lock-in
Three steps to runtime security
No SDKs to integrate. No code to change. Just deploy and protect.
Deploy the Proxy
Run the Silker proxy as a Docker container. One command, no dependencies, no code changes to your app.
docker run silkerai/proxyTraffic Flows Through
Point your traffic to the proxy. Every request and response is inspected in real-time. Threats are blocked before reaching your app.
user → proxy → your appMonitor & Respond
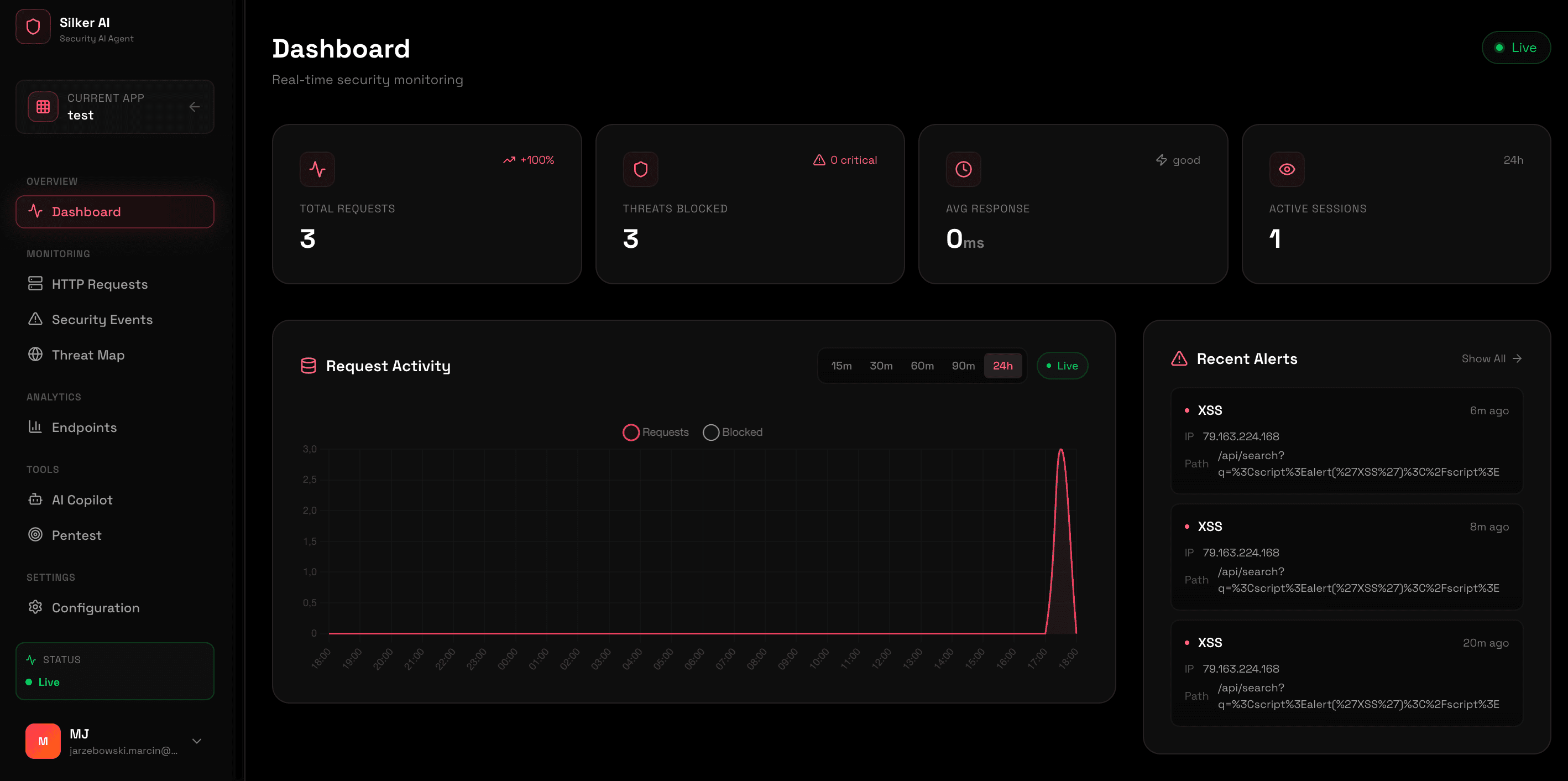
See blocked threats, traffic patterns, and data leak alerts in the dashboard. AI Copilot suggests fixes for detected vulnerabilities.
dashboard.silkerai.comComplete Runtime Security Platform
Reverse proxy that inspects every request and response. Blocks threats in real-time, detects data leaks, and learns your API automatically.
Reverse Proxy Protection
Deploy as a Docker container in front of any application. Inspects all traffic without code changes. Works with every language and framework.
- OWASP Top 10 ProtectionSQLi, XSS, SSRF, CSRF, path traversal, prompt injection and more.
- Response InspectionDetects PII leaks, exposed API keys, and excessive data in responses.
- Auto API Schema LearningLearns your API structure and flags anomalous requests automatically.
Automated Pentesting
Offensive security on demand. Scan your running applications for vulnerabilities without manual configuration. Works with any stack.
- Vulnerability ScanningChecks for open ports, misconfigurations, and exposed secrets.
- DNS & Subdomain EnumMaps your attack surface to find hidden entry points.
- Detailed ReportsGet actionable PDF/HTML reports with fix recommendations.
Monitoring & Alerts
Centralized dashboard with real-time visibility. View blocked threats, analyze traffic patterns, track geographic origins, and get notified of critical issues.
Simple pricing for runtime security
Start free, upgrade as you grow. Deploy as Docker proxy or Cloudflare Worker.
Perfect for side projects
- 1 application
- Up to 10k requests/mo
- Real-time threat blocking
- Community support
For production applications
- Unlimited apps & requests
- Response inspection & PII detection
- Automated Pentesting (Weekly)
- AI Copilot & Priority Support
For large organizations
- On-premise proxy deployment
- Custom SLA & Contracts
- Dedicated Security Engineer
- SOC2 Compliance Reports
Quick start guide
Deploy the proxy in front of your app in under 2 minutes.
1. Run the Proxy
Pull and run the Silker proxy container:
docker run -d \
-p 8080:8080 \
-e SILKER_TARGET=http://localhost:3000 \
-e SILKER_API_KEY=sk_your_key \
silkerai/proxy2. Point Traffic
Route traffic through the proxy instead of directly to your app:
# Before: users -> your-app:3000
# After: users -> silker:8080 -> your-app:3000
# That's it. Your app is now protected.
curl http://localhost:8080/api/healthDocker Compose
Add Silker to your existing docker-compose.yml:
services:
silker:
image: silkerai/proxy:latest
ports:
- "8080:8080"
environment:
- SILKER_TARGET=http://app:3000
- SILKER_API_KEY=sk_your_key
depends_on:
- app
app:
build: .
expose:
- "3000"Trusted by security teams
"Runtime monitoring gave us complete visibility into our application security. We prevented 15+ potential incidents in the first month."
"The auto-fixes saved our weekend. Silker AI detected and patched a SQL injection vulnerability automatically without any downtime."
"Silker AI caught a zero-day exploit in our production API before it could cause damage. The AI-powered detection saved us from a major breach."
"Runtime monitoring gave us complete visibility into our application security. We prevented 15+ potential incidents in the first month."
"The auto-fixes saved our weekend. Silker AI detected and patched a SQL injection vulnerability automatically without any downtime."
"Silker AI caught a zero-day exploit in our production API before it could cause damage. The AI-powered detection saved us from a major breach."
"Runtime monitoring gave us complete visibility into our application security. We prevented 15+ potential incidents in the first month."
"The auto-fixes saved our weekend. Silker AI detected and patched a SQL injection vulnerability automatically without any downtime."
"Clear, trustworthy security reports across the org. We detected and blocked 200+ suspicious activities in our first quarter."
"Slack integrations were seamless. Security alerts reach our team instantly, saving us critical response time during incidents."
"Support is outstanding. Every security question had a thoughtful answer within minutes. They understand our threat landscape."
"Clear, trustworthy security reports across the org. We detected and blocked 200+ suspicious activities in our first quarter."
"Slack integrations were seamless. Security alerts reach our team instantly, saving us critical response time during incidents."
"Support is outstanding. Every security question had a thoughtful answer within minutes. They understand our threat landscape."
"Clear, trustworthy security reports across the org. We detected and blocked 200+ suspicious activities in our first quarter."
"Slack integrations were seamless. Security alerts reach our team instantly, saving us critical response time during incidents."
"Support is outstanding. Every security question had a thoughtful answer within minutes. They understand our threat landscape."
"Silker AI transformed our security posture. Zero-trust implementation was seamless, and we've eliminated data breaches entirely."
"Predictive threat detection gave us early warnings about emerging attack patterns. We stayed ahead of cyber threats."
"Compliance reporting became effortless. SOC2 audits are now automated, saving us weeks of manual work each quarter."
"Silker AI transformed our security posture. Zero-trust implementation was seamless, and we've eliminated data breaches entirely."
"Predictive threat detection gave us early warnings about emerging attack patterns. We stayed ahead of cyber threats."
"Compliance reporting became effortless. SOC2 audits are now automated, saving us weeks of manual work each quarter."
"Silker AI transformed our security posture. Zero-trust implementation was seamless, and we've eliminated data breaches entirely."
"Predictive threat detection gave us early warnings about emerging attack patterns. We stayed ahead of cyber threats."
"Compliance reporting became effortless. SOC2 audits are now automated, saving us weeks of manual work each quarter."
Secure your application today
Deploy the proxy in 2 minutes. No code changes, no vendor lock-in. Start blocking threats immediately.